Quantum Security Solutions
Preparing your organization for the quantum computing era with advanced Post-Quantum Cryptography implementations that safeguard your most critical communications and data.
The Quantum Threat Landscape
Quantum computers pose an existential threat to current cryptographic systems. When sufficiently powerful quantum computers emerge, they will be capable of breaking RSA, ECC, and other widely-used encryption methods in hours or days rather than millennia. This isn't a distant future concern—the time to act is now.
NIST-Approved PQC Algorithms
We implement only NIST-standardized Post-Quantum Cryptographic algorithms, ensuring your systems meet federal compliance requirements and industry best practices.
🔐 CRYSTALS-Kyber
Key Encapsulation Mechanism (KEM)
Based on lattice cryptography, providing secure key exchange resistant to both classical and quantum attacks.
• Small key sizes
• NIST Category 1 security level
✍️ CRYSTALS-Dilithium
Digital Signature Algorithm
Lattice-based signatures ensuring authenticity and non-repudiation in quantum-safe communications.
• Strong security guarantees
• Suitable for high-volume applications
🌐 SPHINCS+
Hash-Based Signatures
Conservative approach using well-understood hash functions for long-term signature security.
• Stateless signatures
• Long-term archival applications
Our Quantum Security Services
📊 Cryptographic Inventory & Risk Assessment
Complete audit of your current cryptographic implementations, identifying vulnerable systems and prioritizing migration based on risk exposure and business criticality.
🔄 Migration Strategy & Planning
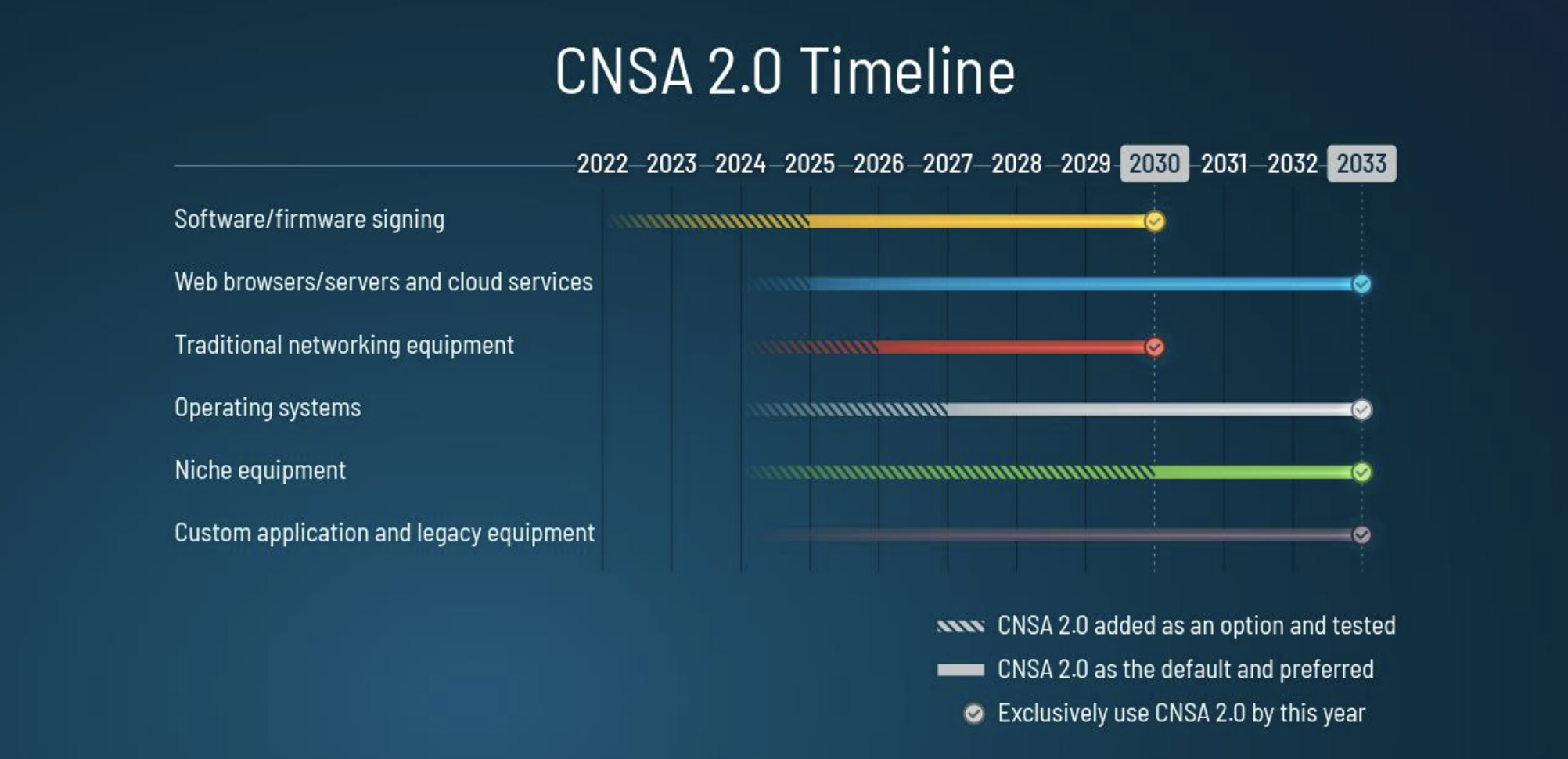
Develop comprehensive roadmaps for transitioning to post-quantum cryptography, including timeline recommendations, resource requirements, and risk mitigation strategies.
⚙️ Hybrid Implementation
Deploy hybrid classical-quantum resistant systems that maintain current security levels while preparing for full PQC transition, ensuring continuous protection.
🧪 Testing & Validation
Rigorous testing of PQC implementations including performance analysis, interoperability verification, and security validation against known attack vectors.
📚 Training & Knowledge Transfer
Comprehensive training programs for your technical teams on PQC principles, implementation best practices, and ongoing security maintenance requirements.
🔍 Ongoing Monitoring & Support
Continuous monitoring of quantum computing developments, algorithm updates, and emerging threats with proactive recommendations for system updates.
Our Implementation Methodology
Discovery & Assessment
Comprehensive analysis of current cryptographic infrastructure and quantum vulnerability assessment.
Strategic Planning
Development of tailored migration roadmap with prioritized implementation phases and risk mitigation.
Pilot Implementation
Controlled deployment of PQC solutions in non-critical systems to validate performance and compatibility.
Full-Scale Deployment
Systematic rollout across all systems with continuous monitoring and optimization throughout the process.
Validation & Testing
Comprehensive security testing, performance benchmarking, and compliance verification of implemented solutions.
Ongoing Support
Continuous monitoring, updates, and support to maintain quantum-safe security as threats evolve.
Don't Wait for Quantum Day
The transition to post-quantum cryptography is not optional—it's inevitable. Organizations that start now will have a significant security advantage and avoid the rush when quantum computers become a reality.
Ready to secure your future?
Contact Tactical Communications LLC today to begin your quantum-safe transformation. Our experts are standing by to assess your current vulnerabilities and design a custom PQC implementation strategy.